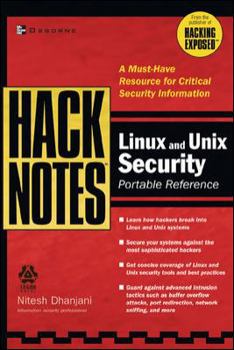
Hacknotes Linux and Unix Security Portable Reference
Select Format
Select Condition 
Book Overview
Helps you to safeguard your systems from all types of hackers, hijackers, and predators. It provides you just-the-facts coverage of Linux, UNIX and Solaris, and helps you learn about advanced hacking... This description may be from another edition of this product.
Format:Paperback
Language:English
ISBN:0072227869
ISBN13:9780072227864
Release Date:June 2003
Publisher:McGraw-Hill/Osborne Media
Length:250 Pages
Weight:0.79 lbs.
Dimensions:0.6" x 6.0" x 9.0"
Customer Reviews
5 ratings
One of the best Unix/Linux security books I own
Published by Thriftbooks.com User , 20 years ago
I own a lot of security books and I try to keep up with what his happening. After reading a few reviews I had been wanting to buy this book until I attended a conference where the author was singing books. So I got my signed copy and I have to say I am pretty impressed with the material. As other people have mentioned here, the author's attitude is to get right to the point and to provide useful examples wherever possible. Part 1 seems to be the where most of the material for this book exists, specially chapter 4 "Remote Hacking". I was pleasantly surprised to read the end of chapter 4 where the author describes how to use my favourite Unix tool Zebedee to do remote port forwarding! I had used this tool to do many things but I wasnt aware how it could be used to perform port forwarding tricks. Hacking tips are arranged in the order of ports and so it is easy to look up vulnerabilities. The entire book is very well arranged . If there is ever a 2nd edition to this book, I will buy it.
Well done
Published by Thriftbooks.com User , 21 years ago
Got this book after I read a recent review. I found this book to contain some pretty cool attack & penetration techniques. Chapters like the one on NASL and the Zaurus PDA hacking are a nice addition. Since this is a hacking book, I disagree with the one review on here that complained about it not being complete. As far as the a & p techniques go, this book packs in more info than most 400+ hacking books I own. Saves a lot of desk real estate and also time. I really dont want to read 5 pages telling me what a portscan is, just tell me how to do it. I prefer it over the Hacking Exposed Linux book when I need quick and precise answers. This book helps me with just this. Right to the point, and some very cool techniques!5 thumbs up.
useful and informative
Published by Thriftbooks.com User , 21 years ago
My favourite section of the book is 'Remote Hacking'which is a good 50 pages long. What I liked about this chapter is that it shows exactly howto use security tools to break into unix and linux servers. The other sections are interesting also. I highly recommend this book.
Short and right to the point
Published by Thriftbooks.com User , 21 years ago
There are quite a few secucity related books out there nowdays. But most of them is just way too thick for me, to make matters worse those books are often filled with repeated or unwanted information. However, this book is different; it cuts right to the point and present me just the right amount of information that I wanted to know. At the same time, it is thin enough so I can carry it around with me. As a unix sysadmin I think this is one of those books that should go right next to the "Unix System Administration Handbook" on bookshelfs. This is a must have book for people who cares or want to know more about security.
Excellent material
Published by Thriftbooks.com User , 21 years ago
The description of this book does not do it justice. I didnt expect much but mainly purchsed it because I liked the sound of the titles of its special chapters in Wireless hacking, NASL programming (for Nessus), and hacking with the Zaurus PDA.At first glance, I wasnt sure how much material was presented. But after reading the first page or two, I realized the the purpose of the book, which is to give to-the-point information on topics such as enumeration, footprinting, remote hacking, privilege escalation, host hardening, etc. I have compared it to the other security books I already own, and this book seems to contain much more information in only about 200 pages! Since I am a sysadmin and have to travel a lot, I carry this book around with me in my laptop bag. I have only owned it for 2 days and have looked it up for reference material a bunch of times already. Good stuff. I highly recommend it, and watch out for the clever hacking techniques and goodies presented in the remote hacking chapter.